Hello Cloud Marathoner’s,
We are continuing our cloud learning journey with Azure services today. Last year Azure Active Directory has introduced many useful features and we will talk about one of them that simplifies the identity governance.
“An Azure Active Directory (Azure AD) entitlement management is an identity governance feature that enables organizations to manage identity and access lifecycle at scale, by automating access request workflows, access assignments, reviews, and expiration. ” – Microsoft Azure AD Identity Governance
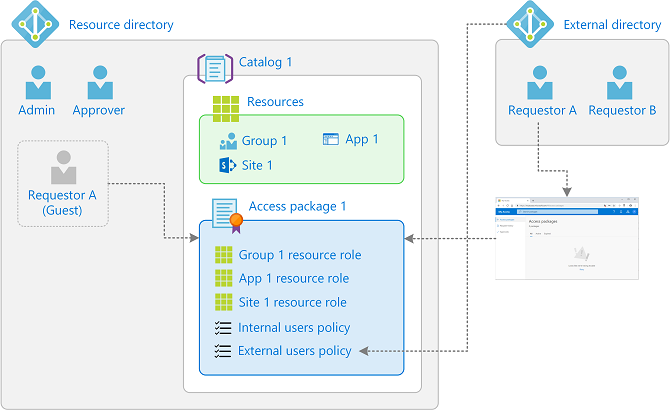
Entitlement management example with one catalog and two access packages
How can entitlement management help?
There are several ways how you could leverage these features for your Azure resource management activities. The easiest one to get started with is the delegation options:
✔️ Delegate management of resources from high privileged account to managers
✔️ Govern access for users in your organization
✔️ Govern access for users outside your organization
✔️ Automate and simplify day-2-day management
✔️ View and report on resource assignments and access packages
Let’s consider following two common scenarios:
First Scenario: As administrator you want to delegate access governance from IT administrators to users who aren’t administrators.
Check out the Video clip for step-by-step guidance.
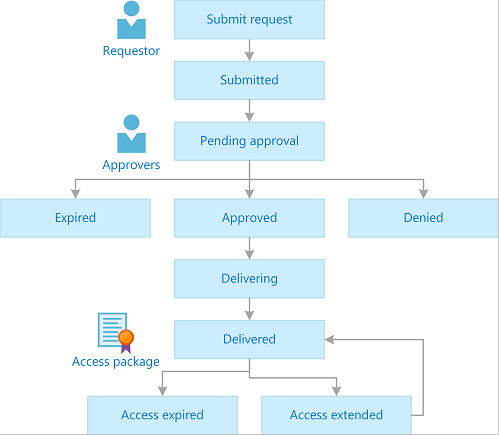
Second Scenario: You would like to create an automated request process for your users to enable them request for an access package (set of Azure resources and accesses rights) to do their job.
The request process of access packages can be simply understood by a help of a following sample infographic.
When I should use access packages?
It is not a silver bullet, so access packages do not replace other mechanisms for access assignment. However, following use-cases are most appropriate in situations where you would consider them:
- Employees need time-limited access for a particular task. For example, you might use group-based licensing and a dynamic group to ensure all employees have an Exchange Online mailbox, and then use access packages for situations in which employees need additional access, such as to read departmental resources from another department.
- Access that requires the approval of an employee’s manager or other designated individuals.
- Departments wish to manage their own access policies for their resources without IT involvement.
- Two or more organizations are collaborating on a project, and as a result, multiple users from one organization will need to be brought in via Azure AD B2B to access another organization’s resources.
Thank you for reading till this point. Stay tuned for more Cloud Security and Administration related posts.
Fᴏʟʟᴏᴡ ᴍᴇ 🎯 ᴀɴᴅ become ᴀ #cloudmarathoner ⛅🏃♂️🏃♀️ – 𝐋𝐄𝐓’𝐒 𝐂𝐎𝐍𝐍𝐄𝐂𝐓 👍
#microsoftazure
#AzureAD
#identitygovernance
#accessmanagement
#secureaccess
#bestpractices
#continuouslearning